Secure hard disk disposal is not just a line item on an IT checklist for businesses across the United States; it's a fundamental component of your corporate risk management strategy. It involves using certified methods like data wiping or physical shredding to ensure sensitive information on retired IT assets is irretrievably destroyed. For commercial entities, this process is a critical defense against data breaches and a mandatory step for compliance with stringent data privacy laws. This guide provides a framework for IT managers and business owners in the United States seeking secure e-waste management solutions.
Why Secure Hard Disk Disposal is a Business Imperative
That storage room filled with decommissioned hard drives is more than just outdated hardware; each device is a potential liability. A single mishandled drive could contain confidential client financial records, proprietary corporate data, or sensitive employee information. A simple oversight in the IT asset disposal (ITAD) process can quickly escalate into a catastrophic data breach, damaging your company’s reputation and bottom line.

The Real-World Consequences for Businesses
The fallout from a data breach caused by improper IT equipment disposal can be staggering. Federal and state regulations like HIPAA, GDPR, and the FTC Disposal Rule carry severe penalties for non-compliance.
Consider these commercial scenarios:
- A healthcare provider discards an old server without certified data destruction, potentially facing millions in HIPAA fines for exposing patient records.
- A financial services firm fails to shred drives from a data center decommissioning, leading to SEC violations, client lawsuits, and a complete loss of trust.
- An enterprise loses its competitive advantage because R&D data was recovered from a laptop that was improperly disposed of during an office cleanout.
Secure disposal isn't an operational expense. It's a strategic investment in risk management and brand protection. It transitions your company from a reactive stance to a proactive data defense posture.
Navigating the Complex Legal Landscape
For businesses in the United States, maintaining compliance with the evolving matrix of data privacy regulations is a significant challenge. The legal onus is on your organization to prove that you took every reasonable measure to protect sensitive data throughout its lifecycle, including its final destruction. This is where partnering with a certified ITAD service for secure hard disk disposal becomes your best defense. For expert legal guidance, consulting a Florida Data Privacy Lawyer for Startups can help navigate these complex requirements.
Learn more about how to protect your company from data breaches with secure data destruction practices in our detailed guide.
Why Certified Destruction is Non-Negotiable for Enterprises
The commercial sector is heavily investing in the hard disk destruction equipment market—valued at an estimated USD 450 million—as companies nationwide work to meet compliance mandates.
With 60% of breaches linked to lost or stolen devices, the necessity for certified, professional IT asset recovery and destruction is clear. This is not a task for internal staff. Partnering with a certified ITAD vendor provides the specialized equipment, secure processes, and auditable documentation required to demonstrate due diligence and protect your business.
Building Your Corporate Data Destruction Strategy
Effective secure hard disk disposal is the result of a deliberate and documented strategy. Before any drive is wiped or shredded, your business needs a clear, actionable plan. This strategy serves as your roadmap for identifying risks, classifying data, and ensuring every data-bearing asset—from data center equipment to individual laptops—is handled correctly from retirement to final disposition.
A robust plan prevents critical oversights, such as forgotten servers in a storage closet or a stack of old workstations from a past refresh. These "forgotten" assets often pose the greatest risk because they fall outside of standard IT lifecycle management. The first step is always a comprehensive audit to create a complete inventory of all IT equipment.
Auditing and Classifying Your Data-Bearing Assets
First, your business must identify every device that stores data. This inventory should extend beyond servers and computers to include a range of commercial equipment.
- Workstations and Laptops: All company-issued machines used by your employees.
- Servers and Data Center Equipment: Including SANs, NAS devices, and blade servers.
- Networking Hardware: Routers and switches can store sensitive configuration data and network logs.
- Printers and Scanners: Modern multi-function devices often have internal hard drives that cache copies of scanned or printed documents.
- Medical and Laboratory Equipment: Specialized devices in these fields frequently contain integrated data storage.
- Mobile Devices: Company-owned phones and tablets are mobile data repositories.
After inventorying, the next step is data classification. Not all data carries the same level of risk. Categorize it based on sensitivity to determine the required destruction method. For instance, a drive from a server processing financial or healthcare records requires a higher level of security than one from a marketing kiosk.
Creating a Formal Data Disposition Policy
A formal data disposition policy eliminates guesswork and ensures consistent procedures across your organization. This document should clearly outline protocols for handling retired IT assets and serve as the definitive guide for your IT, facilities, and procurement teams.
Your policy must define:
- Data Classification Levels: (e.g., Public, Internal, Confidential, Restricted).
- Required Disposal Method for Each Level: Specify whether certified wiping is sufficient or if physical destruction is mandatory.
- Chain-of-Custody Procedures: Detail the process for tracking assets from the moment they are decommissioned.
- Documentation Requirements: Mandate the collection of a Certificate of Data Destruction for every disposed asset.
This policy is your internal framework for compliance and risk management. As you develop this plan, ensure your data backup strategies are current. Using the best external hard drive for backup ensures critical data is preserved before the source media is destroyed.
A well-defined data disposition policy is your first line of defense. It transforms secure hard disk disposal from an ad-hoc task into a systematic, repeatable, and auditable business process that protects your company.
By mapping your assets and setting clear rules, you can make informed decisions based on your company’s risk profile, ensuring no device is overlooked. To learn more, see our guide on making data destruction easy with these 5 steps.
Choosing The Right Destruction Method: Wiping vs. Shredding
Once you have inventoried your retired data-bearing assets, you must decide how to destroy the data. This is a strategic decision that balances security requirements, asset value, and compliance mandates.
The two primary methods for secure hard disk disposal are certified data wiping and physical shredding. Each has a specific role in a comprehensive ITAD strategy for commercial enterprises.
The choice depends on your objective for the hardware. Are you aiming for IT asset recovery to recoup value from newer equipment? Or is your top priority ensuring data on an obsolete drive can never be recovered? Answering this question is the first step toward a secure and cost-effective process.
Certified Data Wiping For Value Recovery
Certified data wiping is a software-based method where every sector of a hard drive is overwritten with random data, often multiple times. When performed correctly according to standards like NIST 800-88, the original data becomes completely unrecoverable.
This is the ideal solution for newer, functional IT assets that you plan to resell or redeploy. By preserving the hardware, data wiping can turn a potential liability into a revenue stream through asset value recovery, supporting a circular economy approach to IT.
For a deeper look at the process, review our guide on how to properly wipe a computer hard drive.
Physical Shredding For Absolute Security
When data sensitivity is paramount and there is no room for error, physical shredding is the definitive solution. This process involves feeding hard drives into an industrial shredder that reduces them to small, mangled fragments of metal and plastic. There is no software and no possibility of data recovery—only complete, irreversible destruction.
Shredding is the mandatory method for:
- End-of-life or failed drives: A drive that cannot be powered on cannot be wiped.
- Drives with highly sensitive data: For financial records, personal health information (PHI), or proprietary intellectual property, shredding provides indisputable proof of destruction.
- Solid-State Drives (SSDs): Due to their flash-based technology, shredding is widely considered the most foolproof method for ensuring complete data eradication from SSDs.
Here's the bottom line: Wiping preserves value, but shredding provides certainty. The most effective corporate ITAD strategies often use a hybrid approach, applying the appropriate method based on the asset's age, condition, and the data it contains.
This decision tree can help visualize the process.
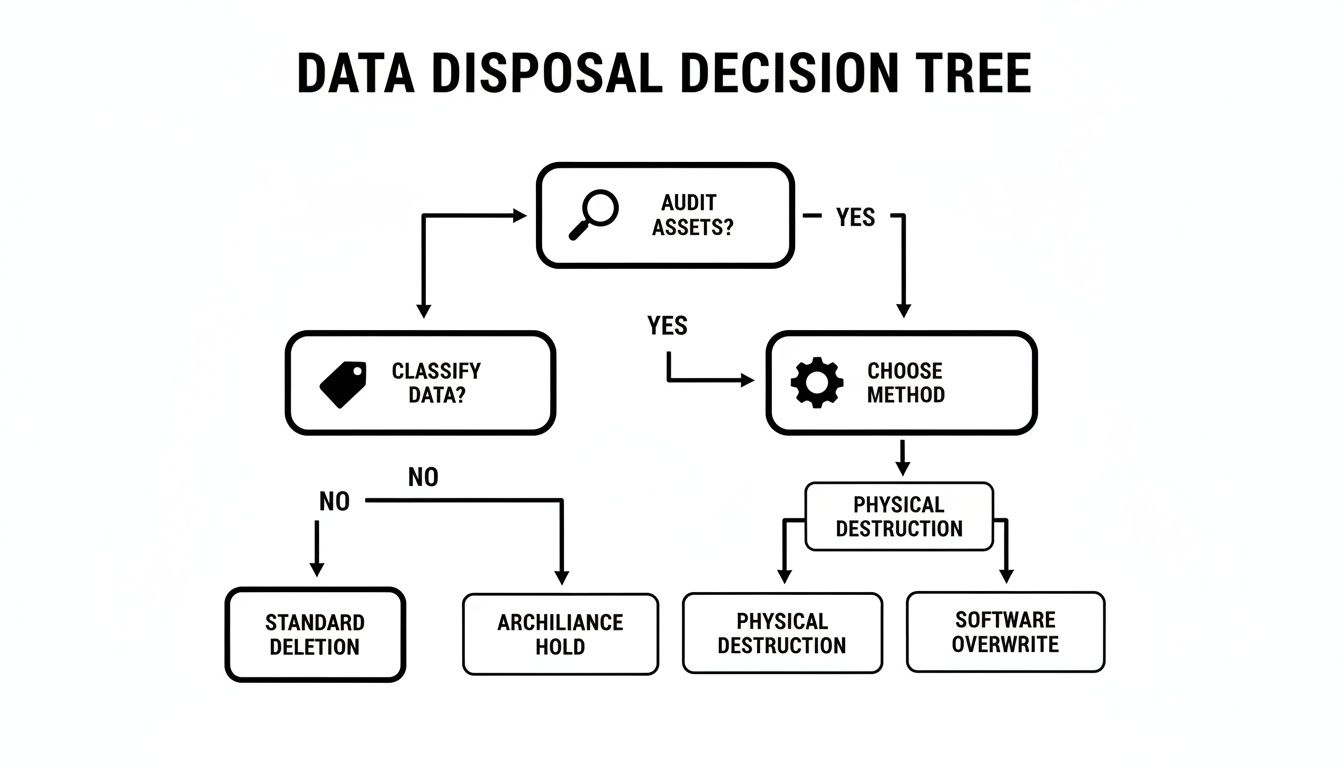
As the flowchart illustrates, the choice follows a logical path after auditing assets and classifying data, ensuring a balance between security and potential IT asset recovery.
Comparison Of Data Wiping vs. Physical Shredding
To make the optimal choice for your organization, a side-by-side comparison is useful. The right decision depends on your business needs, risk tolerance, and goals for retired hardware.
| Factor | Certified Data Wiping (NIST 800-88) | Physical Shredding |
|---|---|---|
| Security Assurance | High; data is rendered unrecoverable by software means | Absolute; the physical media is destroyed, making data recovery impossible |
| Asset Reuse | Yes; the hardware remains fully functional and intact | No; the hardware is completely destroyed and cannot be reused |
| Value Recovery | High; allows for resale, redeployment, or donation | None; the asset's only value is as scrap material |
| Compliance Suitability | Excellent for most regulations (HIPAA, GDPR, FTC) | The ultimate proof for regulations requiring total destruction |
| Typical Cost | Moderate; involves labor and software licensing | Varies; can be lower for bulk, but may have higher logistics costs |
In practice, the best strategy is often a combination of both. A business might choose to wipe and resell a batch of three-year-old laptops while having older servers from a data center decommissioning shredded.
Partnering with a certified ITAD provider like Beyond Surplus allows you to implement a flexible, compliant program that maximizes asset value while providing ironclad security for every retired drive.
On-Site vs. Off-Site Destruction: Logistics and Security
After deciding between wiping and shredding, the next question is where the destruction will occur. This decision impacts security oversight, logistics, and your compliance strategy. Choosing between on-site and off-site services requires aligning the destruction process with your organization's risk tolerance and operational needs.
The core concept governing this choice is the chain of custody: the documented, unbroken trail that tracks your sensitive hard drives from your facility to their verified destruction. A weak link in this chain represents a potential data breach.
On-Site Destruction: Maximum Visibility and Control
With on-site destruction, the entire process is brought to your business location. A specialized, mobile shredding truck arrives at your facility, and your hard drives are destroyed immediately at your loading dock or in the parking lot. The primary benefit is the absolute peace of mind that comes from witnessing the destruction firsthand.
This method is often the required standard for organizations in highly regulated sectors like healthcare, finance, or government contracting.
Key advantages of on-site destruction for businesses include:
- Witnessed Destruction: Your IT or facilities manager can personally observe as each drive is inventoried, scanned, and fed into the shredder, leaving no doubt about its disposition.
- Unbreakable Chain of Custody: Assets never leave your secure perimeter until they are destroyed, creating the shortest and most secure chain of custody possible.
- Immediate Compliance: This is the most direct way to satisfy compliance frameworks that mandate witnessed destruction.
The primary trade-off is typically cost, as mobilizing specialized equipment and a professional crew can be more expensive than off-site processing.
Off-Site Destruction: Efficiency Built for Commercial Volume
In an off-site destruction model, a certified ITAD partner provides secure logistics for collecting your assets and transporting them to their specialized, secure facility for processing. While you don't witness the destruction yourself, a reputable vendor offers a rigorous and transparent process to guarantee security. This is often the more efficient and cost-effective option, especially for large-scale IT retirement, computer recycling, and data center decommissioning projects.
A secure off-site process is not a black box. It is a meticulously documented journey designed to provide the same level of security assurance as on-site services.
To ensure an ironclad chain of custody, the following protocols are essential:
- Serialized Inventory: Each hard drive's serial number is scanned and recorded at your location before transport.
- Secure Transport: Drives are sealed in locked, tamper-evident containers for transit.
- GPS-Tracked Vehicles: The transport vehicle is monitored via GPS from your facility to the destruction plant.
- 24/7 Facility Security: The destination facility is secured with video surveillance and strict access controls.
Choosing a certified partner like Beyond Surplus ensures these protocols are rigorously followed. Explore our professional hard drive destruction services to see how we maintain a secure chain of custody for every commercial client.
Verification: The Final Step in Secure Hard Disk Disposal
Once your hard drives have been handed over for disposal, the process is not complete. Your organization is not fully protected until you have official documentation in hand. For secure hard disk disposal, verification is the critical final step that closes the liability loop. Without documented proof, you cannot validate your compliance in an audit or legal setting.
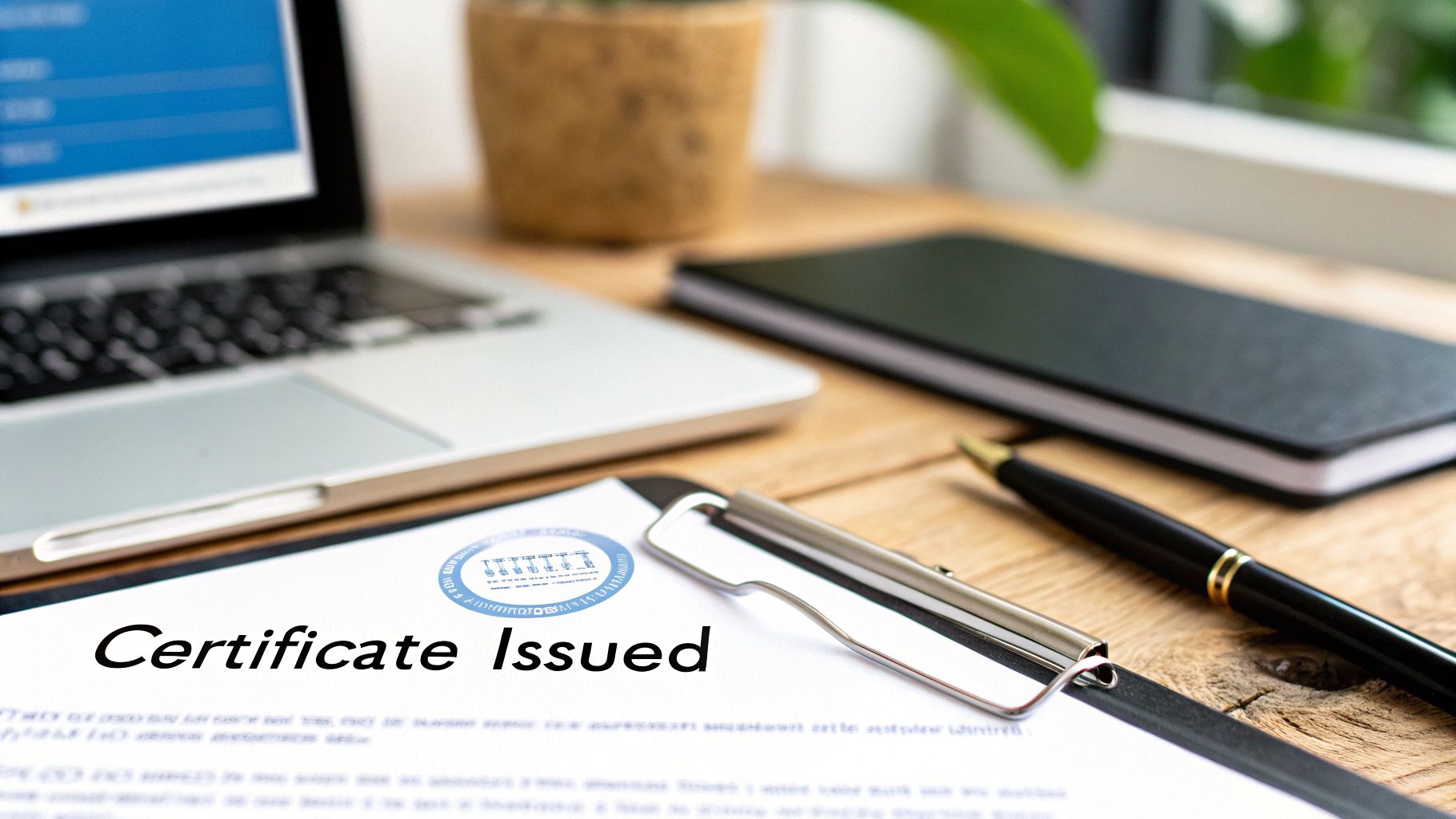
This final stage is centered on documentation. A professional ITAD partner's role is not just to destroy hardware but also to provide the auditable evidence that proves the job was done correctly. This documentation is your safeguard and tangible proof of due diligence.
The Certificate of Data Destruction Is Non-Negotiable
The most critical document you will receive is the Certificate of Data Destruction (CoDD). This is a legally significant document that formally transfers liability for the data from your company to the ITAD vendor. It serves as your definitive proof of compliance with regulations like HIPAA, FACTA, and the FTC Disposal Rule.
A legitimate CoDD must contain specific, auditable details to be valid:
- A Complete Asset List: Every drive must be listed by its unique serial number, creating a direct link between your inventory and the destruction record.
- Method of Destruction: The certificate must specify how the data was destroyed—whether via NIST 800-88 compliant wiping or physical shredding.
- Chain of Custody Details: It should document the process, including the date and location where the final destruction occurred.
- Official Attestation: The document must be signed and certified by an authorized representative of the ITAD company.
The absence of these elements renders the certificate ineffective as a compliance tool. To understand what a proper document includes, you can review the components of a professional hard drive destruction certificate.
Holding Your Vendor Accountable
This documentation empowers you to hold your ITAD partner accountable. Before engaging a vendor, request a sample of their Certificate of Data Destruction and verify that it includes all necessary details. A transparent, professional provider will readily comply with this request.
Your Certificate of Data Destruction is the legal firewall that protects your business. It is the official record proving you took every necessary step to securely manage end-of-life data, mitigating risk and completing the asset lifecycle.
This final verification step transforms the concept of "data security" into a provable action, ensuring your secure hard disk disposal process is both effective and defensible.
Finding a Certified ITAD Partner for Your Business
Selecting a partner for secure hard disk disposal is a critical vendor decision for any enterprise. You are not merely hiring a hauling service for old equipment; you are entrusting a vendor with your company's most sensitive data and its reputation.
The right ITAD partner functions as an extension of your security and compliance teams. The wrong one can become your greatest liability. The decision must be based on verifiable certifications, robust security protocols, and a transparent process that withstands scrutiny, not just on price.
Look for Industry-Leading Certifications
Certifications are the most important initial filter. They provide independent, third-party validation that a vendor adheres to strict standards for data security, environmental responsibility, and operational excellence.
The two most critical credentials in the commercial ITAD industry are:
- R2v3 (Responsible Recycling): The leading global standard for electronics recycling, an R2v3 certification confirms a vendor's commitment to environmentally sound practices, worker safety, and a secure chain of custody.
- e-Stewards: Another highly respected certification focused on preventing the illegal export of hazardous e-waste. It guarantees your retired IT assets will be managed responsibly from pickup to final disposition.
A vendor holding both certifications operates at the highest level of the industry.
Vet Their Security and Insurance Policies
After verifying certifications, investigate the specifics of their security measures and liability coverage. A verbal assurance is insufficient when a data breach could result in millions of dollars in damages.
A trustworthy ITAD partner operates with full transparency. They should readily provide clear documentation of their security protocols, insurance coverage, and downstream recycling partners.
Ask direct questions about their policies:
- Insurance Coverage: What are the limits of their data breach and pollution liability insurance? Ensure the coverage is sufficient to protect your organization in a worst-case scenario.
- Facility Security: How do they secure their processing facility? Look for 24/7 video surveillance and strictly controlled access.
- Employee Screening: Do they conduct thorough background checks on all employees who handle sensitive media? This is a non-negotiable security measure.
Understand Their Downstream Process
Finally, you must know what happens to your assets after processing. A certified vendor is required to maintain a transparent downstream recycling chain, tracking all materials to their final destination. This is essential for environmental compliance and protecting your brand's reputation.
The demand for vendors providing this level of assurance is growing rapidly. The global hard drive destruction service market was valued at USD 1.65 billion and is projected to reach USD 5.05 billion by 2035. This growth is driven by businesses seeking partners who can meet stringent regulatory demands. You can discover more insights about this growing market on SphericalInsights.com.
Choosing a partner like Beyond Surplus, who holds these critical certifications and offers comprehensive commercial services from data center decommissioning to IT asset recovery, ensures your entire disposal strategy is built on a foundation of trust and verifiable compliance.
Your Top Hard Disk Disposal Questions, Answered
Even with a detailed plan, specific questions often arise before an IT asset disposal project begins. Addressing these final details can mean the difference between a good disposal process and a truly secure and compliant one. Here are the questions we hear most frequently from our commercial clients across the United States.
Is Deleting Files or Formatting a Drive Sufficient for Business Use?
Absolutely No. Deleting files or performing a standard format on a hard drive only removes the directory pointers to the data. The underlying information remains intact and can be easily recovered with widely available software. This is unacceptable for any commercial or enterprise application.
For genuine data security, businesses have two professional-grade options:
- Certified Data Wiping: Uses specialized software to overwrite every sector of the drive according to strict standards like NIST 800-88.
- Physical Destruction: The drive is fed into an industrial shredder and physically destroyed, making data recovery impossible.
What is a Certificate of Destruction, and Why Does My Business Need One?
A Certificate of Data Destruction is a formal, auditable document provided by your ITAD vendor that serves as an official record of destruction.
This certificate is your legal shield. It transfers liability away from your organization and provides the essential proof of due diligence required by regulations like HIPAA, FACTA, and the FTC Disposal Rule.
A legitimate certificate for business use must include the unique serial numbers of each asset, the specific destruction method, the date of destruction, and an official signature.
Are SSDs Disposed of the Same Way as Traditional Hard Drives?
While both require secure handling, their underlying technologies are different. Software designed for traditional hard disk drives (HDDs) can be unreliable on Solid-State Drives (SSDs) due to features like wear-leveling and over-provisioning, which can leave data remnants behind.
For this reason, physical destruction is the gold standard and most reliable method for SSDs. A certified ITAD partner will use industrial shredders capable of destroying both magnetic HDDs and flash-based SSDs, ensuring complete data annihilation for all media types, including laptop disposal and computer recycling.
Navigating the complexities of data destruction is non-negotiable for protecting your business. Beyond Surplus provides certified, secure, and compliant solutions for electronics recycling and IT equipment disposal designed for commercial and enterprise clients across the United States. Contact us today for certified electronics recycling and secure IT asset disposal.