You probably have the same problem many telecom teams run into after a network refresh. Pallets of routers, switches, transport gear, access devices, and retired spares are sitting in a cage or staging room. Finance wants recovery value. Security wants proof that nothing leaves the site without controls. Operations wants it gone without disrupting live services.
That’s where most organizations lose money. They treat decommissioned gear like waste too early, or they hand it to telecom equipment buyers before they’ve organized the assets, isolated data-bearing devices, and defined terms. A better process turns surplus hardware into a managed disposition project with three goals: recover value, reduce risk, and keep logistics clean.
Initial Asset Preparation and Inventory Management
Disorganized collections kill quotes. If a buyer receives “miscellaneous Cisco, Juniper, and optical gear,” you’ll get a soft estimate at best and a discounted one in practice. Buyers pay for clarity.

Build the inventory before requesting bids
Start with a line-item asset register. Capture model number, serial number, installed modules, power supplies, optics, rails, license-relevant accessories, cosmetic condition, and whether the unit powers on. Separate installed gear from loose spare inventory. Keep photos attached to the record for anything high value or physically damaged.
An initial audit matters for more than resale. Future Market Insights notes that hardware accounts for 51.70% market revenue, and it also warns that ignoring virtualization capabilities can create up to a 22% scalability gap when repurposing hardware. That matters when deciding what should be resold, redeployed internally, or broken down for parts.
A practical inventory usually sorts into these buckets:
- Network edge gear such as routers, switches, firewalls, and carrier access equipment
- Transport equipment including optical platforms, shelves, transceivers, and related modules
- Compute and support systems such as servers, appliances, and management hardware
- End-of-life scrap candidates with damage, missing components, or no viable secondary demand
Flag data-bearing assets early
Telecom teams often underestimate where data lives. It isn’t just in servers. Carrier appliances, unified access devices, voice systems, and some switching platforms can retain configs, call data, credentials, or customer information. Pull those devices into a controlled stream before any equipment leaves for testing or resale.
Practical rule: If you can’t confirm whether a device stores data, treat it like it does until your disposition plan says otherwise.
Strong inventory work also makes the rest of the lifecycle easier. If your team needs a process framework, this guide to effective corporate asset management is useful for aligning finance, operations, and risk controls. For organizations building a broader retirement workflow, IT asset lifecycle management should connect procurement, deployment, reuse, and final disposition instead of treating end-of-life as a one-off event.
The Landscape of Telecom Equipment Buyers
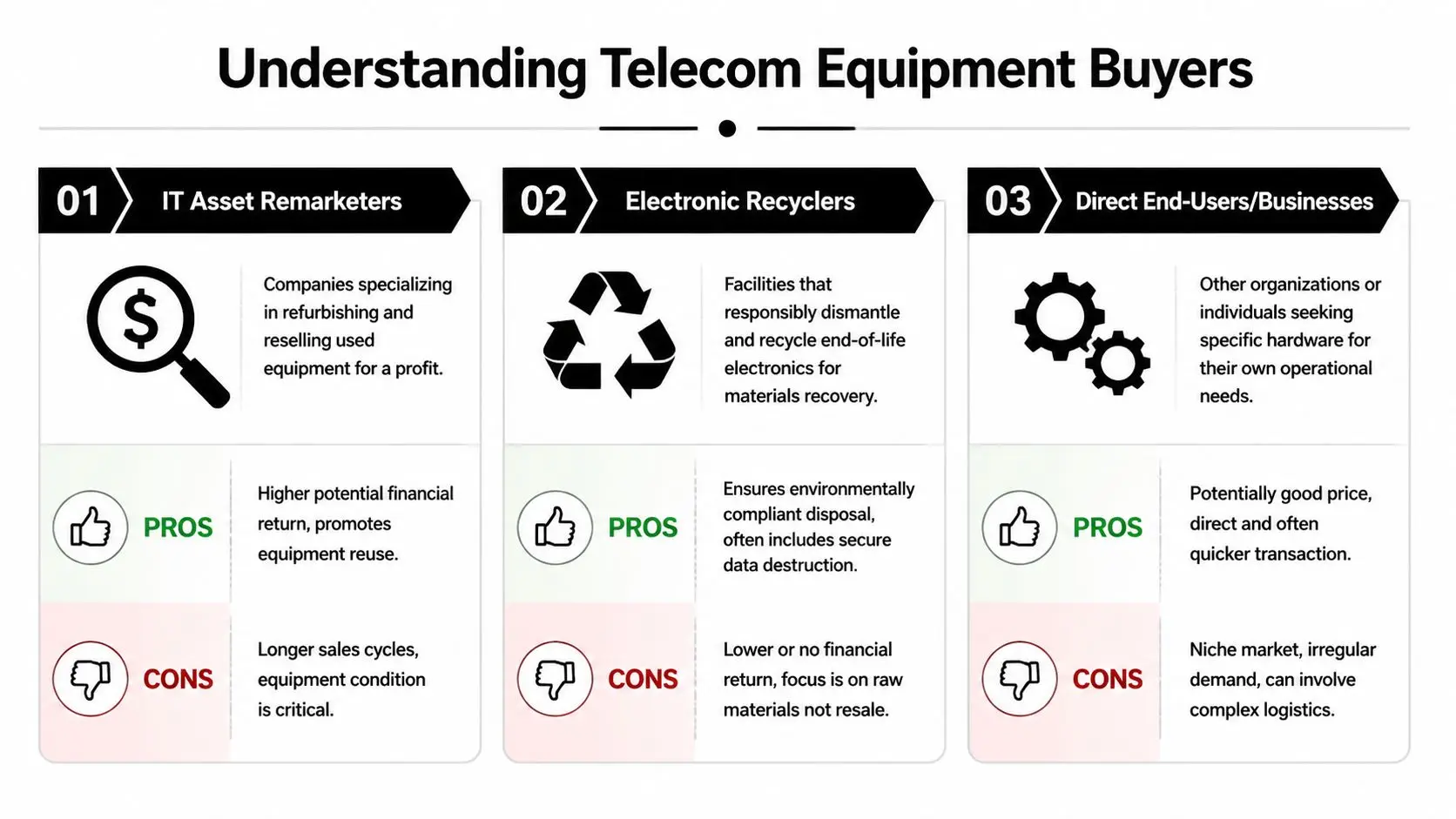
Not all telecom equipment buyers solve the same problem. Some maximize resale. Some minimize risk. Some make disposal easy but leave money on the table.
The market behind buyer demand
Telecom operators remained the primary buyers in 2025, taking 71.25% of the telecom equipment market, while enterprise private 5G is projected to grow at 14.62% CAGR from 2026 to 2031 according to Mordor Intelligence. For sellers, that means two things. Carrier refreshes still drive large secondary supply, and enterprise demand is broadening the pool of buyers for reusable equipment.
Three buyer types that matter
| Buyer type | Best fit | Main strength | Main risk |
|---|---|---|---|
| ITAD firm | Mixed lots with compliance needs | Security, logistics, reporting | May not offer the highest price on every premium SKU |
| Specialist broker | Clean, marketable telecom lots | Strong resale focus | Narrow acceptance criteria |
| OEM trade-in program | Refresh tied to new purchases | Simplicity | Credit can be restrictive |
ITAD firms work best when the project includes data destruction, serialized reporting, pickup coordination, and recycling for unsold units. This model is efficient for enterprise teams that don’t want separate vendors for resale, destruction, and scrap handling.
Specialist brokers can produce strong offers on sought-after routers, switches, optics, and telco spares when the list is clean and the condition is known. They’re less useful when the lot contains damaged gear, mixed generations, or compliance-heavy assets.
OEM trade-in programs can make sense during a planned upgrade. The trade-off is control. Credits are often tied to future purchases, and proprietary rules can narrow what counts toward the return.
A high offer on a spreadsheet means very little if the buyer excludes half the lot after inspection.
One option in the first category is a compliance-focused provider listed among IT asset disposition companies. The right choice depends on your asset mix, internal security requirements, and whether your priority is cash recovery, speed, or liability transfer.
How to Secure Accurate Equipment Valuations
Valuation breaks down when sellers ask for a “scrap number” on equipment that still has reuse potential. In a flat market, that mistake is expensive.

Worldwide Supply notes that telecom equipment spending fell 11% year over year in 2024 and no recovery was expected through 2025, which makes value recovery from decommissioned gear more important. In that kind of environment, secondary-market trade-ins and buybacks can reduce capital pressure without requiring new purchases.
What buyers actually price
Buyers don’t value a part number in isolation. They price the package around it.
- Configuration completeness matters. A chassis with line cards, matching power supplies, fan trays, and blanks usually prices better than an incomplete unit.
- Condition changes the channel. Clean tested gear goes toward resale. Damaged or incomplete gear often drops into parts harvest or commodity recycling.
- Demand determines speed. Common enterprise networking gear may move steadily. Niche carrier hardware can bring value, but only with the right buyer and a realistic timeline.
How to get better quotes
Ask for a fair market value assessment, not just a blanket pickup number. Provide the inventory in spreadsheet form, attach photos, identify whether packaging is available, and state which assets require certified data destruction before remarketing.
Use at least two quote styles. One should be a straight buyout. The other should separate resale candidates from recycle-only material. That tells you whether the buyer understands the list or is averaging risk into a lower offer.
When a quote looks unusually high, check the deductions. Freight, testing fallout, data destruction, and recycling fees often show up later.
If you need an outlet for marketable gear, selling telecom equipment works best when your asset list is detailed enough for buyers to distinguish reusable inventory from low-value material.
Executing Ironclad Data Destruction and Ensuring Compliance
This is the point where many otherwise profitable projects fail. A telecom asset can have resale value and still be a compliance problem. If the device stores customer information, credentials, network configs, or regulated records, security controls come first.

Refresh activity is constant. GM Insights reports that the global telecom services market reached 1.37 trillion USD, and that sectors including BFSI at USD 193.56 billion in 2024 face frequent equipment refresh cycles. The same source notes that secure disposal through certified ITAD partners is essential for transferring liability and complying with FTC rules.
Match the destruction method to the asset
A one-method approach usually creates waste or risk.
- Software wiping fits devices where validated sanitization is practical and the organization wants to preserve resale value.
- Degaussing is useful for certain magnetic media, but it can render assets unusable for remarketing.
- Physical destruction is the right call when policy, device condition, or data sensitivity leaves no room for doubt.
For regulated organizations, the method isn’t enough by itself. The process must be documented, repeatable, and auditable.
What the paper trail must include
A valid disposition record should identify the asset, the custody handoff, the sanitization or destruction method, the processing date, and the final outcome. The document most buyers and auditors care about is the certificate. Without it, you may have completed the work operationally but failed to close the risk administratively.
The certificate is not a courtesy document. It is the evidence that your organization followed through.
Use standards-driven language internally. Teams evaluating sanitization workflows should understand NIST SP 800-88 because it provides a practical framework for deciding when to clear, purge, or destroy. That decision should be tied to the type of media, the sensitivity of the data, and whether the asset is meant for reuse.
Healthcare, finance, education, and government teams should also insist on auditability from pickup through final processing. If a vendor can’t explain its documentation flow in plain terms, that’s a warning sign.
Streamlining Logistics and Maintaining Chain of Custody
A strong quote can still unravel during pickup. The trouble usually starts when equipment is moved in bulk without serialized tracking, sealed packaging, or documented handoff.

That problem is getting harder during infrastructure transitions. Wireless Estimator notes that copper-to-fiber migrations create significant chain-of-custody challenges for legacy infrastructure in the U.S., especially as programs like the Rural Digital Opportunity Fund accelerate fiber rollouts and copper retirements.
What good logistics looks like
The pickup team should arrive with an asset list, labeling plan, packaging materials, and a defined route for controlled loading. Loose stacking is a mistake for both security and value recovery. Damage in transit turns resale inventory into parts inventory quickly.
For larger removals, the custody record should capture:
- Serialized handoff records tied to each asset or sealed container
- Packaging control including pallets, crates, seals, or tamper-evident labeling
- Transport accountability showing who released, moved, received, and processed the load
Why chain of custody matters
Chain of custody isn’t just a legal phrase. It’s the operating document that explains where each asset went and who touched it. If an auditor, customer, or internal security team asks what happened to a retired router, shelf, or copper-heavy legacy component, you need a clean answer backed by records.
The standard should be simple. No undocumented pickups. No mixed loads without reconciliation. No “we’ll sort it out at the warehouse” language.
Comparing Offers and Negotiating Favorable Terms
The best telecom equipment buyers rarely win on price alone. They win on net recovery after deductions, clean scope definitions, and paperwork that closes risk.
Start by comparing offers side by side on five points: purchase price, logistics cost, data-destruction scope, recycling treatment for no-value items, and payment timing. A lower headline offer can still be the better deal if it includes pickup, serialized reporting, and final certificates without hidden offsets.
Terms worth negotiating
Some terms matter more than people expect:
- Inspection windows should be limited so assets don’t sit in limbo.
- Exception handling should say what happens to failed units, missing modules, and recycle-only material.
- Liability transfer language should be clear enough for legal and compliance review.
- Reporting cadence should be defined before pickup, not after.
Use a simple rule when choosing between buyback and recycling. If the gear has realistic resale demand and can be processed securely, pursue recovery. If it’s obsolete, damaged, proprietary, or uneconomical to test, certified recycling is usually the cleaner decision.
Vendor review needs discipline. This vendor due diligence checklist is a useful way to pressure-test claims before you sign a purchase agreement or release equipment. Price matters. Terms matter more when the lot is large, mixed, or sensitive.
When your team needs a practical path from decommissioning to value recovery, Beyond Surplus can support business clients with telecom equipment buyback, secure data destruction, logistics coordination, and certified recycling documentation. Contact them to evaluate your retired telecom assets, reduce disposition risk, and turn surplus gear into a controlled financial recovery project.



