A lot of IT directors end up in the same place. A storage room fills with decommissioned PBX gear, routers, handsets, line cards, gateways, and switches that nobody wants in production anymore, but nobody wants to throw away either. Finance wants recovery. Operations wants the floor space back. Security wants proof that nothing leaves the building with recoverable data. Procurement wants a clean process and a clean paper trail.
That’s why “where to sell telecom equipment” is the wrong question if you stop at price alone. The better question is which channel gives you the best total outcome once you include resale value, labor, freight, chain of custody, and compliance exposure.
The answer changes based on volume, condition, and risk. A few low-risk items can move through broker or marketplace channels. A real business disposition usually needs a tighter process.
The Challenge of Surplus Telecom Equipment
The typical surplus telecom project doesn’t start with a sales strategy. It starts with a refresh, a site closure, a carrier migration, or a voice platform change. One week the equipment is active. The next week it’s sitting on shelves with old asset tags, mixed cables, missing power supplies, and no clear owner.
That creates four competing pressures at once.
- Recover value: Working enterprise telecom gear can still have resale demand.
- Clear space: Retired equipment consumes rack space, cage space, and warehouse space.
- Control data risk: Telecom gear may retain configs, logs, credentials, call data, or network information.
- Document compliance: Regulated organizations need records, not assumptions.
A common mistake is treating all retired gear the same. An old lot of desk phones isn’t the same as edge devices, voice gateways, or network appliances that may still hold sensitive information. Another mistake is waiting too long. Equipment that sits untouched tends to lose completeness first. Power adapters disappear, modules get separated, rails vanish, and valuation drops.
If your internal team is trying to decide whether to sell, recycle, redeploy, or scrap, start with a formal disposition path, not a pile-by-pile cleanup. That’s the practical reason many companies first define the process through IT asset disposition planning before they contact any buyer.
The fastest way to lose money on retired telecom gear is to let it become orphaned inventory.
Selling to IT Asset Disposition (ITAD) Companies
For most organizations, the most defensible answer is a professional IT asset disposition company. An ITAD firm doesn’t just buy equipment. It manages the whole chain: intake, audit, valuation, logistics, data destruction, downstream resale, and recycling for anything that no longer has remarketing value.

That matters because the secondary market is not small or informal. The telecom equipment market is projected to reach USD 749.32 billion by 2036, growing at a 7.5% CAGR. That growth is tied to 5G upgrades and enterprise network expansion, which means organizations keep replacing functional equipment and feeding a real refurbishment market.
What ITAD companies actually do
A qualified ITAD partner usually handles work your internal team would otherwise absorb:
- Asset triage: Separating resale candidates from scrap.
- Serialized inventory: Recording make, model, and condition.
- Data handling: Wiping, shredding, or otherwise processing data-bearing components.
- Pickup coordination: Moving equipment without breaking chain of custody.
- Settlement reporting: Showing what was resold, recycled, or destroyed.
That’s a different service model from a broker who finds a buyer.
Why companies choose ITAD even when another channel might pay more on paper
The highest apparent resale number is not always the highest return. Telecom dispositions fail financially when staff spends weeks sorting mixed lots, packing gear incorrectly, handling buyer disputes, or disposing of the unsold remainder through a second vendor. One coordinated disposition often beats a fragmented one.
A professional ITAD route is strongest when you have:
Mixed inventory
Some assets have resale value. Others don’t. One vendor can process both.Sensitive environments
Healthcare, finance, government, education, and multi-site enterprises need records that stand up in review.Operational deadlines
Moves, closures, and refreshes don’t leave much room for trial-and-error selling.
One example in this category is IT asset disposition companies that combine buyback, certified destruction, and recycling under one scope of work. Beyond Surplus is one such option for organizations that need pickup, secure processing, and value recovery in the same project.
Operational reality: The cleanest disposition process is usually the one with a single accountable party from pickup through final reporting.
Using IT Brokers and Online Marketplaces
IT brokers and online marketplaces can work, but only in narrower situations. They’re not interchangeable with ITAD, and problems start when companies assume they are.

A broker usually sits between seller and buyer. They know demand for brands like Cisco, Mitel, Avaya, and Nortel, and they can help place equipment faster than an internal team with no channel relationships. A marketplace gives you direct control over listings and price, but you handle the labor and the risk.
Where brokers help
Brokers can be useful when the lot is fairly clean and commercially attractive. If you already know the inventory, the condition, and the configuration, a broker may move it without forcing your team to create dozens of public listings.
That said, broker transactions still require internal oversight. You need to confirm what’s included, how equipment will be tested, who handles freight, and what happens to units that fail inspection.
Where marketplaces break down
Marketplaces look attractive because they suggest direct access to end buyers. In practice, business telecom gear often sits longer than expected unless it’s common, complete, and priced carefully.
Here’s the hidden workload many teams underestimate:
| Channel | Upside | Main downside |
|---|---|---|
| Broker | Access to buyers and bulk movement | Less control over final margin and process |
| Marketplace | Full pricing control | Listing, packing, disputes, shipping, unsold leftovers |
| Direct ITAD | One managed workflow | Less suited to maximizing each individual unit price |
Marketplace selling becomes painful when you have to test every handset, photograph every module, answer technical questions, pack odd-shaped equipment, and manage returns. It’s even worse when the lot contains anything data-sensitive.
- Good fit: Small, low-risk lots with no compliance burden.
- Weak fit: Multi-site refreshes, mixed enterprise inventory, or anything requiring certified destruction.
- Poor fit: Large lots with time pressure.
If you want to understand how reusable gear gets remarketed after processing, it helps to review examples of used telecom equipment for sale so you can see what buyers expect in terms of completeness and condition.
How to Accurately Value Your Used Telecom Equipment
Most sellers either overestimate telecom value because the gear was expensive when purchased, or underestimate it because it looks dated. Neither view is useful. Its value comes from market demand plus execution quality.
The biggest rule is simple. Telecom equipment valuation is non-linear. For dispositions of 50+ units, ITAD vendors and IT brokers deliver superior outcomes through bulk pricing efficiency and logistics, and working systems in original configuration command “complete value” while partially functional or stripped systems depreciate significantly.
What buyers actually look at
Condition matters, but not in a generic sense. Buyers usually care about five practical details:
Brand and model
Cisco, Avaya, Mitel, Nortel, and similar brands tend to have clearer resale channels than obscure hardware.Configuration completeness
A chassis with matching cards, faceplates, power supplies, and accessories is easier to resell than a partial unit.Functional status
Working pulls are worth more than untested gear. Untested equipment often gets priced defensively.Cosmetic state
Heavy wear doesn’t always kill value, but broken ports, bent metal, cracked plastics, and missing labels create friction.Market timing
Recently displaced gear can still have active demand. Equipment that has fallen too far behind current standards may move only as parts or scrap.
How to protect value before sale
Most value loss happens before the buyer ever sees the equipment.
- Keep assemblies intact: Don’t separate cards, handsets, power supplies, and mounting hardware unless you know the market prefers it.
- Label lots clearly: Site, rack, and asset data help with audit and resale.
- Avoid rough removals: Improper de-installation damages ports, bezels, rails, and resale confidence.
- Don’t mix scrap with reuse candidates: A pallet of mixed quality lowers bid clarity.
Practical rule: If your team has to ask whether a lot should be sold piece by piece or as one project, you probably need a bulk valuation exercise.
Bulk pricing often produces a better business result because it lowers labor, simplifies pickup, and reduces the number of failed sales. That’s the logic behind structured IT equipment resale programs in Georgia and nationwide enterprise buyback projects more broadly.
Navigating Critical Security and Compliance Mandates
Telecom equipment is often treated as “network gear” instead of “data-bearing equipment.” That distinction is where companies make expensive mistakes. Many telecom assets store far more than people assume: admin credentials, IP schemes, call routing data, user information, logs, voicemail components, and configuration backups.
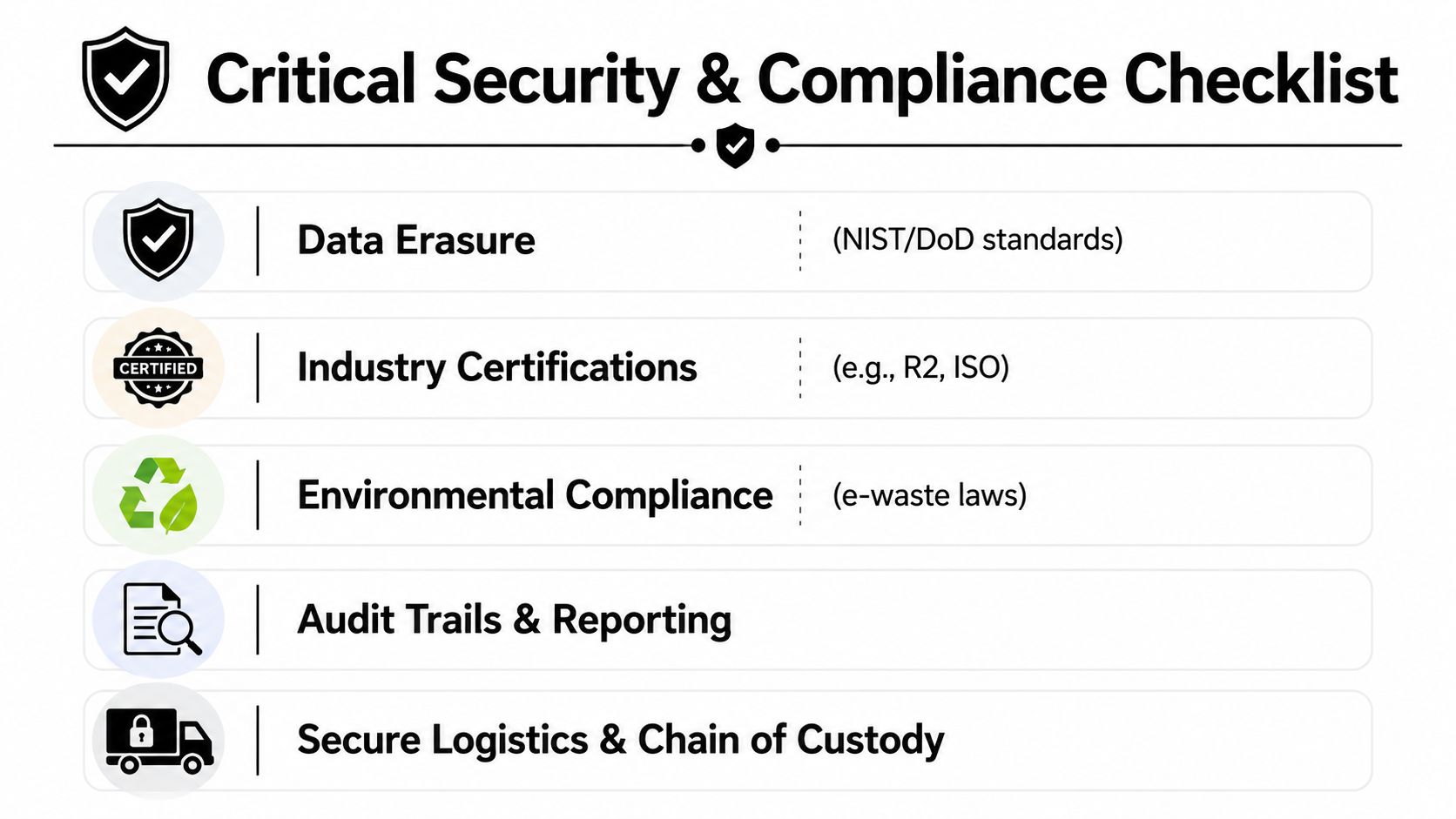
If your company has compliance obligations, this is not a side issue. It’s the core decision point.
Why certification changes the risk profile
That’s the operational difference between a certified ITAD partner and a general buyer. A general buyer may pay for gear. A certified ITAD vendor can issue defensible documentation.
What to require before anything leaves your control
Ask for these items upfront, not after pickup:
Documented chain of custody
You need a record of who handled the assets and when.Defined data sanitization method
Wipe, shred, or destroy should be specified by asset type.Certificates after processing
A verbal assurance is not enough for audit purposes.Downstream accountability
You need to know who processes non-resalable material.
A useful way to think about this is through the broader lens of strategic GRC for CIOs. Asset disposition sits inside governance, risk, and compliance. It isn’t separate from it.
What goes wrong with informal buyers
The problem with informal channels isn’t just that they lack paperwork. It’s that they often lack process discipline. Equipment may be picked up with no formal intake, no serialized audit, and no clear destruction path for failed units. Once that happens, your team can’t reconstruct events later.
Here’s a practical screening checklist:
| Question | Why it matters |
|---|---|
| Can the vendor document chain of custody? | Without it, you can’t prove control over the assets. |
| Can they issue certificates of data destruction and recycling? | Those records support compliance and liability transfer. |
| Do they follow a recognized sanitization standard? | Your security team needs a defined method, not assumptions. |
| Can they manage both resale and non-resale material? | Split streams create tracking gaps. |
For organizations that need standards-based sanitization language, NIST SP 800-88 guidance is often the right reference point for internal policy alignment.
If a buyer can’t explain their chain of custody in plain language, they shouldn’t be handling your retired telecom equipment.
Managing Logistics From Pickup to Payout
The sale itself is only one step. The operational burden sits in the movement of the assets.

Many internal teams underestimate how much value can be lost between rack removal and buyer receipt. A line card bent during removal, a gateway shipped loose, or a pallet wrapped poorly can erase recovery before the settlement report is written.
The actual work in a telecom disposition
A business-grade telecom removal usually includes all of the following:
De-installation
Someone has to power down, disconnect, and remove equipment safely.Inventory capture
Assets need model verification, quantity checks, and exception notes.Packing and palletizing
Telecom gear is not all ship-ready in the condition it comes out of service.Freight coordination
Pickups need scheduling, handling instructions, and destination control.Receipt and reconciliation
Quantities and condition get checked on arrival.Settlement
Resale credits, recycling records, and destruction certificates have to line up.
Where DIY projects go off track
DIY dispositions usually fail in one of three places.
Internal labor gets underestimated
Your network or facilities team becomes a shipping department.Packaging is improvised
That invites damage claims and price reductions.Custody records are incomplete
Then compliance questions show up after the project is closed.
Even the paperwork side can become messy. If your company deals with cross-border shipments or complex carrier documentation, resources on freight documentation like critical paperwork for importers can be useful background. The point isn’t to turn your IT team into logistics specialists. It’s to understand why logistics discipline matters.
What good logistics support looks like
Strong disposition logistics should include:
On-site coordination
Clear pickup windows and named contacts.Secure handling
Assets don’t sit exposed in a loading dock queue.Condition-aware packing
Reusable equipment is protected like inventory, not scrap.Reporting continuity
The item count at pickup should connect cleanly to the final report.
Good logistics protects both value and evidence. Bad logistics destroys both at the same time.
A Strategic Framework for Choosing the Right Partner
Where to sell telecom equipment depends less on category labels and more on the shape of your project. The channel that works for ten low-risk handsets is not the channel that works for a multi-site voice migration.
The broader market supports that reality. North America contributes approximately 38.1% to global telecom equipment market growth, and the mature U.S. market produces a consistent flow of enterprise-grade equipment for remarketing. In practical terms, there are buyers. The harder question is which kind of buyer fits your risk profile.
A simple decision framework
Use this matrix internally before you approve any disposition path.
| Your situation | Likely fit |
|---|---|
| A few low-risk items, no sensitive data, no urgency | Marketplace may work |
| Clean lot of commercially desirable gear, limited compliance burden | Broker can work |
| Mixed lot, multiple locations, data concerns, reporting requirements | Certified ITAD is the strongest fit |
| 50+ units or regulated environment | Certified ITAD should be the default |
Questions to ask before selecting any partner
Vendor selection here is really a third-party risk exercise. Procurement and security teams should treat it that way. Frameworks on mastering third-party risk assessment are useful because they force the right questions before a project starts.
Ask every potential partner:
- What assets do you buy directly, and what do you broker out?
- How do you handle equipment that fails testing?
- What documentation do you issue after processing?
- Who controls transportation and chain of custody?
- Can you support both reuse and compliant recycling in one workflow?
What usually works best in the real world
For business telecom dispositions, the winning choice is rarely the channel with the highest theoretical resale number. It’s the one that gives you acceptable recovery with controlled risk and manageable effort.
Marketplace selling works when the project is small enough to tolerate friction. Brokers work when the lot is attractive and the process burden is still manageable. A certified ITAD approach makes the most sense when the project has any real complexity, especially when legal, security, and operations all have a stake in the outcome.
The right partner should help you defend the decision to finance, security, and leadership. That means they should be able to explain value recovery, custody, destruction, reporting, and downstream handling without hand-waving.
Conclusion Your Next Steps for Secure Telecom Asset Recovery
Selling retired telecom hardware is not just a resale exercise. It’s a business process that touches asset recovery, security, logistics, and compliance at the same time. The best path depends on what you’re holding, how fast it has to move, and how much risk your organization can accept.
If you only have a few low-risk items, a marketplace or broker may be enough. If you’re managing a larger lot, a mixed inventory, or any environment with compliance obligations, a certified ITAD workflow is usually the responsible choice. That approach reduces internal workload, preserves more value through proper handling, and gives your organization the documentation it needs after the equipment leaves the building.
The practical next step is simple. Build an inventory list, identify any data-bearing assets, flag anything incomplete or damaged, and decide whether this is a resale project, a compliance project, or both. Most enterprise telecom dispositions are both.
Contact Beyond Surplus for a no-obligation review of your retired telecom equipment, secure data destruction requirements, and value recovery options.